Hacking IPTV, or why default passwords are bad.
Unchanged vendor default passwords are bad. That might seem obvious, but it's amazing how frequently default passwords seem to turn up...
More and more of the hotels I stay at use some form of IP-based system for the in-room TV. Many of these use IPTVs, but a small number use external Set-Top Boxes (STB) of various forms.
Whilst recently staying in a hotel in Asia that used an external STB I decided to do some digging into the system to see how secure it was. The results were, as you can probably guess from the default password comment above, very interesting.
The first target was the STB itself. The box itself was branded as "2M-Locatel", which led to some interesting details on the web, but nothing that helped actually access it. Next step was to get my hands on a small ethernet switch (US$7 at a local computer store!) to allow me to get my computer on the network at the same time as the STB. From there it didn't take much to find the IP of the STB, and discover that it allowed telnet access.
More importantly, the banner message when connecting with telnet stated that the STB was actually an "Amino" brand. Back to Google, and in a few minutes I had the full users guide for a similar Amino STB, including the details for the default root password :
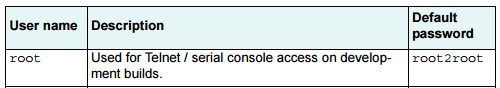
The "development builds" comment didn't leave me all that hopeful, but I can't say I was overly surprised when I typed in the password and landed at a root prompt!
Step 1 Complete - root access on the STB in my room!
Root on the STB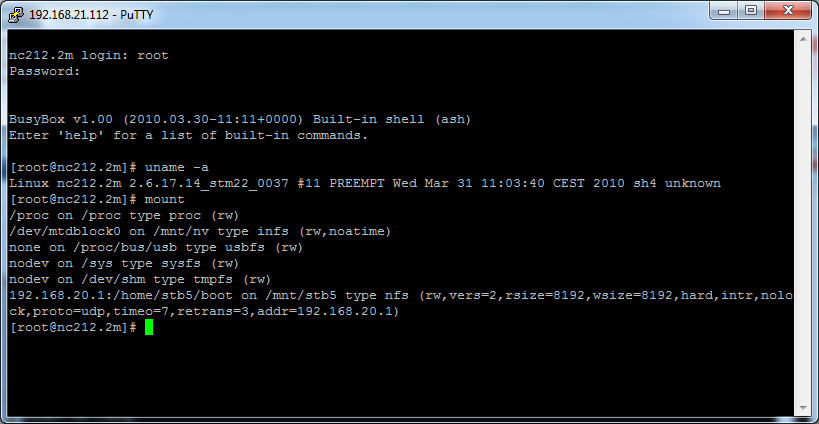
Of course, what works on one STB should also work on the rest of the STBs in the hotel - presuming that the network would actually let me connect to them. Picking an IP address one higher than that from the STB in my room, I found I was also able to telnet to that system, and again login with the same root password.
Step 2 Complete - root access on every STB in the entire hotel!
Looking around on the STBs showed that they were pretty much stateless, and were setup to NFS mount a directory from a server who's address they got via DHCP. That directory contained the binaries that were run to function as an IPTV, as well as some very basic configuration infromation - but unfortunately nothing very helpful.
However the server the NFS mount was coming from did appear interesting. Unlike the STB's this system didn't allow telnet access, but it did allow ssh - although not surprisingly the root password from the STB's didn't work this time.
Whilst previously search for details regarding 2M-Locatel I had managed to find some Debian Preseed files that appeared to be used to setup some form of systems, and burried deep in those files were two passwords - one for an account called "nice", and another for a the "root" account.
# Root password, either in clear text
d-i passwd/root-password password SofieW d-i passwd/root-password-again password SofieW
# To create a normal user account.
d-i passwd/user-fullname string nice d-i passwd/username string nice
# Normal user's password, either in clear text
d-i passwd/user-password password fin1vms d-i passwd/user-password-again password fin1vms
You can probably guess what happened next - logging in as "nice" worked, and then su to "root" worked, both using the default passwords from the preseed files!
Step 3 Complete - root access on the IPTV Server!
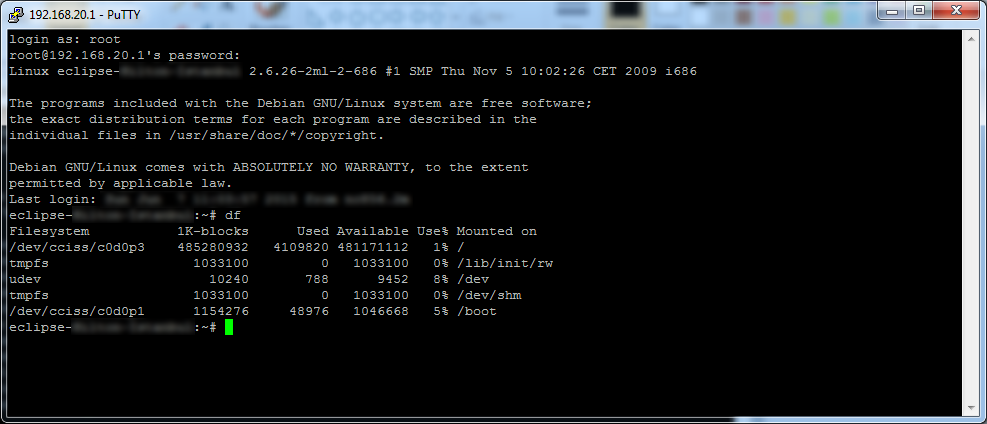
Accessing the same server IP via a web browser presented a login screen for "Eclipse", but this time I didn't know a username/password, so this was a dead end for the moment.
Running on the server, among other things, was a Postgres database. With root access no password was required to access postgres, and to find that there was a table called "users". Although the passwords in this table were encrypted it did show the usernames for all of the users, including a few local users - plus one called "nice". Back to the web interface, and not at all surprisingly the password for the "nice" account was the same as the unix account of the same name. What's more, this account appeared to be a full admin account!
Step 4 Complete - full access to the Web Interface!
The web interface gave clean and simple access to everything. From STB details and configuration, to guest details including name and room number for everyone staying in the hotel, billing information for pay-per-view movies (including the ability to change the price of such movies, or swap Toy Story for a Playboy movie!). At this point I had full control over the entire hotels IPTV system.
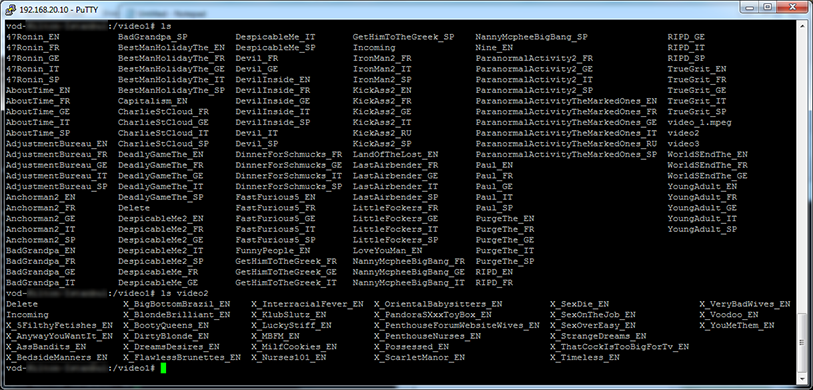
The web interface also referenced a Video-on-demand server on a different IP. The "nice" account didn't work on this one, but the default "root" password did, giving access to a few hundred gigs of DVD-Rip movies without having to pay the ~US$15 each to access them.
Step 5 Complete - full access to download all of the on-demand movies!
At one point when logging into the main server I'd noticed a "Last Login from ..." message with an public/Internet IP address. Making an outbound internet connection easily got me the IP address being used for outgoing connection, and connecting back to that IP address showed that both the SSH and web interfaces were fully accessible from the Internet.
Step 6 Complete - full access to the entire environment from anywhere in the world!
So to summarize, this entire environment is fully accessible from anywhere on the internet, using default passwords, for both the Unix shell (as root) and the web interface (as an admin user). A user anywhere in the would could carry out any action, from downloading movies, to recording occupancy rates and guest names, to falsely generating charges for on-demand movies - or just simply reformatting the entire environment taking it completely offline, likely for days or longer.
Having found these problems I attempted to contact the relevant staff at the hotel, however multiple emails to the General Manager, the Front Office Manager, and one of the Duty Managers have gone unanswered. Despite their lack of action I've decided not to name the hotel or even the country - other than to say that it's somewhere in Asia.